Indistinguishability Obfuscation (iO) 💻#
Indistinguishability Obfuscation is a powerful cryptographic primitive designed to obscure the internal workings of a program while fully preserving its functionality.
Core Concept: Functionally Equivalent code 🔄#
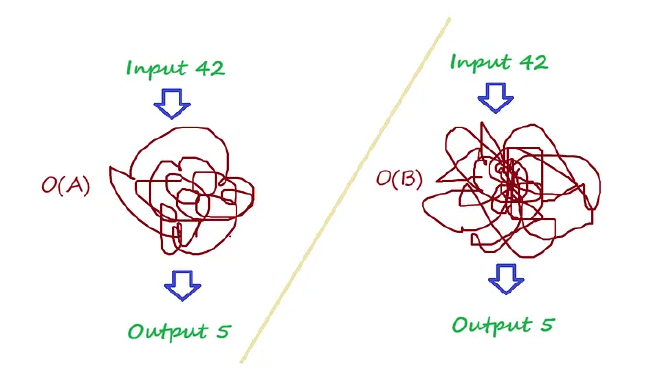
Consider two distinct computer programs, \(A\) and \(B\).
- They produce identical outputs 🎯 for every possible input.
- This means that for any input \(x\), \(A(x) = B(x)\).
- Crucially, their internal logic or algorithms may differ significantly. For example, they could be two different implementations of the same sorting algorithm.
The Obfuscation Process 🛡️#
When an Indistinguishability Obfuscator (let’s denote it as \(O\)) is applied:
- Program \(A\) is transformed into an obfuscated version: \(O(A)\).
- Program \(B\) is transformed into an obfuscated version: \(O(B)\).
The “Indistinguishable” Property Defined ❓#
The obfuscation is formally “indistinguishable” if:
- For any two functionally equivalent programs \(A\) and \(B\), the obfuscated versions \(O(A)\) and \(O(B)\) are computationally indistinguishable.
- This implies that no polynomial-time adversary can distinguish between \(O(A)\) and \(O(B)\) with a probability significantly better than guessing.
- From a computational standpoint, it is impossible for any adversary to determine whether an obfuscated program \(O(P)\) (where \(P\) is either \(A\) or \(B\)) was derived from the original program \(A\), or if it was derived from program \(B\).
Key Implication: Irreversibility & Security 🔐#
This strong property has a critical consequence:
- The obfuscation process is effectively irreversible.
- This ensures that any embedded “secrets” within the original program’s logic (e.g., proprietary algorithms, secret keys, intellectual property) remain completely hidden and unrecoverable from the obfuscated code. 🔒
I found this video for a mathematical introduction to this topic:
🔗 youtube: Indistinguishable Obfuscation Explained#
With all the other interesting cryptographic measures we have (zero-knowledge proofs, homomorphic encryption). The future of certain tech implementations will be really interesting.
Thank you for reading
first new page post, nice !

